How Continental managed to test a large safety module with 18,000 lines of code (LoC) within only one week.
Industry
Automotive
Department
Development
Size
> 230 000 Employees
Location
Hannover, Germany
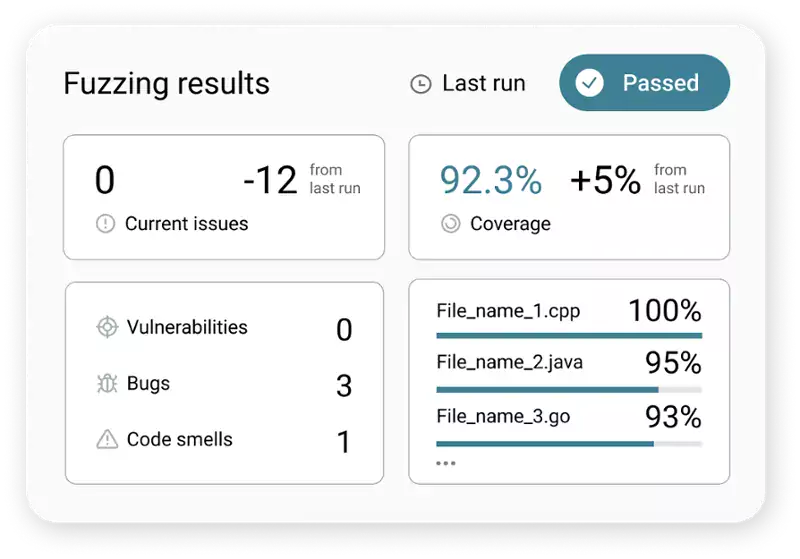
The Results
Developing Secure Infotainment Systems Faster
"Only 1% of all our security tests done for the project where CI Fuzz was used were fuzz tests, but through them, we find about 57% of all vulnerabilities."
Victor Marginean
Former Global Head of Cybersecurity & Privacy Business Unit HMI // Continental

Challenges
1. Realizing Modern Security Tests in An Embedded Automotive Architecture
Continentals HMI business unit develops embedded systems and solutions for the human-machine interface of modern road vehicles. For example, display solutions, head-up displays and cockpit high-performance computers. HMI makes processing and managing information simple, intuitive, and reliable.
Infotainment systems in modern vehicles usually communicate with a whole range of external embedded sensors. These dependencies add an additional layer of complexity for security testing, as they typically require plenty of manual effort.
Writing Test Harnesses
Hardware Dependencies
2. Complying With ISO 21434/UNECE WP.29
As a result of the new ISO/SAE 21434 and UNECE WP.29, many car producers (OEMs) are extending their software testing activities. The standard holds regulations for software devices within vehicles, along with their connectivity to external systems.
Implementing Fuzz Testing
How to Get the Developers on Board
The Solution
CI Fuzz Testing Platform
Continental implemented the CI Fuzz testing platform in their CI/CD to improve their code quality and development speed. CI Fuzz is a CI/CD-agnostic platform for automated security testing. The platform helps developers protect themselves against unexpected edge cases. It empowers them to fix bugs during development and to achieve reproducible testing results.








The Success
Fuzzing Embedded Systems With Dependencies
The CI fuzz testing platform makes it possible to apply modern fuzz testing approaches in an early stage of the software development process. This has automated and simplified the entire testing process because it enabled the developers to perform security tests on their own modules and to fix critical bugs right away.
The CI Fuzz testing platform also enabled the developers to mock their hardware with fuzz data. By applying feedback-based fuzzing many developers at Continental are now able to protect their software against edge cases and unexpected behaviors. For example, if a sensor should send unusual or erroneous inputs.
Get Started With CI Fuzz
Implementing CI Fuzz helped Continental to significantly improve the quality and security of their software while getting them one step closer to ISO 21434 compliance. If you want to evaluate how CI Fuzz can help you develop secure software faster, explore our guided product tour or feel free to book an exploration call with one of our colleagues.