Fuzzing Web Applications
Automated fuzz testing is one of the best ways to secure complex web applications.
Learn how to apply this approach to your own projects.
Automated REST API Testing in 5 Easy Steps
Learn how to automatically test REST API endpoints and critical API parameter combinations in this recorded live coding session.
In this live coding session, Daniel Teuchert presented best practices that will help you find more vulnerabilities through automated REST API testing.
What To Expect:
- Why Is it Important to Secure Web Applications?
- 4 Challenges of Securing Web Services?
- Implementing Test Automation to Deal With Complexity
- Securing Web Applications With Feedback-Based Fuzzing
- What Bugs Can Fuzzing Find in Complex Web Services?
- Advantages and Limitations of Web Application Fuzzing
Why Is it Important to Secure Web Applications?
A 2021 study showed that 50% of all data breaches begin with web applications. Modern web applications have many independent microservices that each has a designated function. The data flow between these services is controlled by APIs (Application Programming interfaces), which account for around 70% of the total web traffic. While this structure is highly effective at handling vast amounts of data requests, it provides plenty of attack surface that has to be protected through thorough security testing.
The Challenges of Securing Web Services
Securing web applications is incredibly challenging. You need to ensure the security of each service and the interaction between them. Developers who want to secure their web services face a variety of challenges.
1. API Endpoint Detection
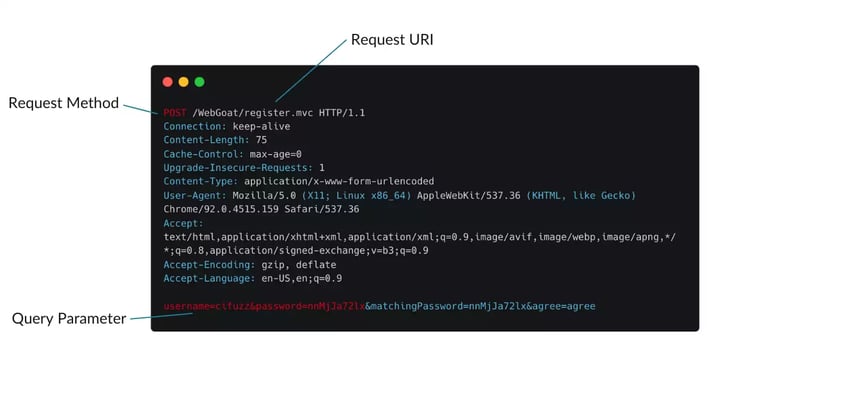
Since APIs manage the communication between web services, they are often the target of external attacks. For example, attackers can exploit vulnerabilities in an API, by injecting malicious inputs that replace valid user interactions. If APIs fail to fully sanitize such inputs before they enter the database, they can cause faulty program states, which can be used to gain unwarranted access or cause downtimes.
To secure web services, API tests have to be able to detect API endpoints and analyze if certain parameter values can cause erroneous program states within them. Since APIs do not have a GUI, this is trickier than it sounds.
2. System Complexity and Multiple Dependencies
Modern web applications communicate with countless other services. Each of these connections could potentially harbor vulnerabilities. If successfully exploited, such vulnerabilities endanger entire microservice architectures. The paths, that enable the communication between these services, can then be used to spread malicious data, as some microservices fully trust inputs from other internal services.
Especially in large projects, weeding through these connections manually is like searching for a needle in a haystack. Even with automated black-box fuzzing tools, i.e. tools that blindly fire huge amounts of inputs into the system, finding vulnerabilities within such vast networks leaves a lot up to chance. The best way to approach such projects is with intelligent algorithms that use refined test inputs and information about the system under test to locate vulnerabilities.
3. Language-Specific Vulnerabilities
Most web service infrastructures are written in Java or other Memory-Safe languages. Although these languages do not have to deal with Memory Corruptions, they are nonetheless susceptible to a variety of dangerous vulnerabilities, including many of the OWASP top 10. How devastating vulnerabilities in web services was recently shown by the log4j vulnerability, which affected countless web applications throughout the world.
4. Test Automation
Since testing the numerous connectivity paths of modern web service architectures manually would require huge amounts of time and resources, most web development teams automate their testing efforts as much as they can. While automated testing approaches make it far easier to uncover web vulnerabilities, their initial configuration is often quite complicated and requires expert knowledge. Especially for large-scale projects, it can be difficult to tailor different testing tools to the given testing environment.
Handling Complexity With Test Automation
The best way to ensure the reliability and availability of your web applications despite their complexity is by implementing automated testing approaches that analyze your web services holistically, including the various communication paths that connect them. Of course, there are several ways to do this. For example, you can implement black-box testing tools, such as OWASP ZAP or Burp Suite. However, feedback-based fuzzing is considered best practice for complex microservice architectures, as it uses the source code to craft highly efficient test inputs.
Securing Web Applications With Feedback-Based Fuzzing
Some modern fuzzing tools are highly automated, to a degree, where developers do not even have to write test harnesses themselves. By using code instrumentation to collect information on how the system under test interacts with test inputs, they can constantly refine test inputs to traverse larger parts of the web service architecture under test. Modern fuzzing platforms can be integrated into any build system, for continuous CI/CD testing.
What Bugs Can Fuzzing Find in Complex Web Services?
As mentioned, feedback-based fuzzing can detect many potentially harmful vulnerabilities, such as XSS-Bugs (Cross-Site-Scripting) and SQL injections. Recently, web fuzzing gained notable attention as it was used to detect the RCE that led to the famous log4j vulnerability. In January, open-source developers were able to find yet another RCE while fuzzing log4j. Click the button below for an overview of the many web vulnerabilities that can be found with feedback-based fuzzing.
Advantages and Limitations of Web Application Fuzzing
A truly big advantage of feedback-based fuzzing is that it can find complex bugs and vulnerabilities that are off-limits to other testing tools. Due to the instrumentation of the source/byte code feedback-based fuzzing platforms can also measure and maximize code coverage, which is one of the most important metrics in web security.
A limitation of web application fuzzing is that it can be quite complex to initially set up, especially with open-source tools. However, most modern fuzz testing platforms have a strong focus on usability, which greatly minimizes the expert knowledge required to get the fuzzer up and running.
Web security expert Daniel Teuchert demonstrates how feedback-based fuzz testing can be used to automatically generate powerful test cases for REST APIs.
Our CTO Khaled Yakdan shows here how feedback-based fuzzing can be used to find vulnerabilities in the backend of your web application. You will also discover how to efficiently detect security vulnerabilities and bugs.
Simon Resch will explain an approach that assists you to simplify and automate your web application testing by implementing modern fuzzing techniques.


